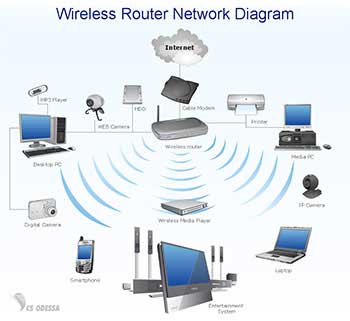
Internet is the essential and wireless networks are accessible to anyone in the modern world. Technology is moving very fast which depends on the internet for everyone machine. Wireless network is widely used in the router’s transmission radius. People are connecting through the public hotspots such as airports, colleges, restaurants and parks. People also use the wireless in their home network to connect multiple devices. Everyday Life people can see the neighbourhood can see the Wi-Fi Network in the system.
You need to know the security key to access the Wi-Fi Network. You can easily connect with the Wi-Fi Network which is secured with password key. You want to connect to these neighbourhood networks. In the internet, people started searching for the Wi-Fi password cracking tools to get the unauthorised access to those wireless networks. People want to check the network usage and analyse the network protocols in it. In the organisations, you want to know the network analyses with the few networking hacking tools which are available to check and analyse packets to see what they’re doing.
People want to explore the Wi-Fi Password with the wireless security to crack with the Tools. We highly recommended this method only educational or testing purposes on your own Wi-Fi only. We will explain the encryption wireless networks use and tools to crack networks to get the
WHAT IS A WIRELESS NETWORK?
In the Wireless Network, you can connect with the Multiple devices in the Network which uses the radio waves to link computers and other devices together. In the electronic devices like Laptop, smartphones and Embedded systems which has the Wireless network enabled in it. WIFI Networks are very easy vulnerable to hacking as wireless signals can be picked and exploited from any where and anyone. Wi-Fi Hacking can be performed by gaining unauthorised access to connect the private Wi-Fi Network.
HOW TO ACCESS WIRELESS NETWORK?
You need to Have the wireless Network enabled devices to connect with the Network such as Laptop etc. you should to be in the Laptop with tools within the transmission radius of the wireless network access point. You should be the most devices of the wireless network option will be turned on in it. you need to provide the list of the available network in it. you can easily to connect with the devices which network is not protected with Password. In case either network is protected with the Password, please follow these steps in mentioned below.
SIMPLE STEPS TO HACK WIFI PASSOWRD
You need to have accessories and tools in the Laptop or system which need to run the application and Move advanced network settings in it. you can see the Many Layers of the Wi-Fi encryption of the Algorithms which are susceptible in the various type of attacks and access to free software tools such as apps found only in the Kali Linux. Here are the other methods which are easily found on the internet on the windows Or Ubuntu will be covered in the Kali Linux in the software used to installed and ready to hack the Password.
TAKE THE CONTROL OF THE NETWORK:
In the first step is the check the network and stay inside your home or place. You have the right place to test the security features and security software. To hack the Network which is illegal to break into other people computing systems which cause big troubles. You can practice on your home network in the system.
TOOLS FOR THE HACK
You need to have the Network and system application in the computer. In the Network, you can see the WAP/WAP2 encryption level which include the following in it. you need to these applications in the system like Kali Linux, Wireless Home router WEP, Aircrack-ng program Kali, wireless USB port Network card, Router for the Network in it.

USB WIRELESS INTERFACE
You need to verify the USB wireless card with the Kali Linux OS software which is very simple open the Bash Shell with command prompt by entering ifconfig in the command. You can see the Multiple Interface in the ethernet interface with the loopback interface with wireless interface with the Name Wlan 0 and wlan 1.
CAPTURE PACKETS
In the command prompt is actually capture packets from the other connected wireless devices in the initiate with the attack. In the software, you will make some comparisons between the captured the packets using the complex algorithm to deduce with the network key issues in the command with the Bash shell.
STORE THE CAPTURE PACKETS
In the next step, you will be storing the captured the pockets from the USB wireless card with the previous command in the several wireless networks with the related information with BSSID channel and other key data. Please enter the Command in the Capture Packets.
.airodump-ng-w[ESSID]-c[Channel]-bssid [BSSID]mon0
You need to Run this command to search this output from the Given wireless in the router’s ESSID channel and BSSID with the point of the reference with the capturing packets which will let it capture the least 10,000 packets before proceeding it. you need to save the following the command to save the captured data with the local HDD.
· airodump-ng mon0 –[file-name]
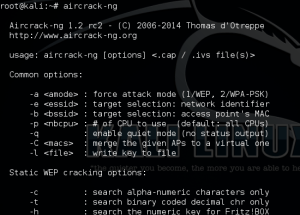
RUN THE AIRCRACK-NG AGAINST THE CAPTURED DATA
You need to Run the cracking software against the all data which you have collected at this point. Run the following the command and plugin with the name of the files which have saved the captured data to.
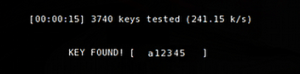
TRY AGAIN TO CAPTURE MORE PACKETS
You need to run these commands in the Linux command with the WEP which will cracking process failed in the collect more packets. You will let the software collect the 15,000 packets and everything should go based on the plan. Wireless will host and capturing the software process will go.
CONCLUSION
You can hack your own Wi-Fi with the WEP encryption which will provide you the Right tools in it. you can hack your Wi-Fi with the Hack tools for the educational purpose and testing purpose. In the Wi-Fi wireless network, you can see the Multiple Networks options in the WPA/WPA2 attack with centred around the multiple passwords after forcing the host to reconnect to it.

